Using Malicious Registrations as a Basis for Blocking Entire TLDs
Colin Strutt
As we analyzed the data for the Interisle Cybercrime Supply Chain 2025 report, we found that some TLDs persistently exhibit an alarmingly high percentage of malicious registrations - domains that were purposely registered by criminals for the purpose of conducting cybercrimes.
To determine whether domain names were purposely (maliciously) registered to perpetrate a cybercrime, we look for domains reported for spam, phishing, or malware within 14 days of domain registrations, domain names that are strikingly similar in composition, domain names that are exceptionally long or have specific composition patterns, and domains that we have determined to be registered using some form of bulk registration.
In a majority of our determinations, malicious domains are reported for phishing, malware, or spam within 14 days of domain registration. Today, we’ll list TLDs with high malicious domains as a percentage of the domains reported for phishing, malware or spam (cybercrime domains), and we’ll discuss the heated topic how to deal with these TLDs.
A Heated Display of Malicious Domains
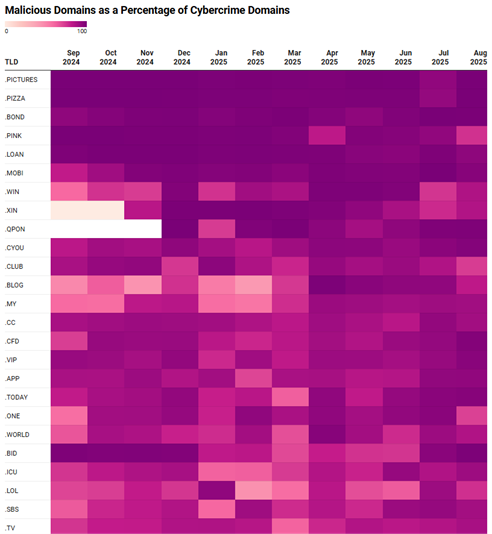
For the period of September 2024 to August 2025, we found 25 TLDs with more than 30,000 cybercrime domains that had more than 80% of their cybercrime domains determined to be maliciously registered.
Below, we use a heatmap (created using Datawrapper) to show the percentage of cybercrime domains each month that were maliciously registered.
A complete table of 54 TLDs that we used to compose the heatmap above is available at DataWrapper. Because of limitations in the availability of domain registration data (a topic we have noted many times before) we believe that our methods undercount the number – and hence percentage – of cybercrime domains that are maliciously registered.
What’s Old is New Again: Most New Domains Are Malicious
Paul Vixie first made this allegation in 2010 in a CircleID post, Taking Back the DNS.
The cybercrime data for September 2022 to August 2023 only had four TLDs with more than 30,000 cybercrime domains of which at least 80% were maliciously registered: .SITE, .TOP, .CFD, and SITE.
The cybercrime data for September 2023 to August 2024 had ten TLDs with more than 30,000 cybercrime domains of which at least 80% were maliciously registered: .CLUB, .LOL, .REST, .VIP, .TOP, .APP, .SBS, .XYZ, .CC, .ICU.
The total number of cybercrime domains in the September 2024 to August 2025 data for the top 25 TLDs is nearly 4.8 million. But those same 25 TLDs from one year earlier had fewer than 1 million cybercrime domains and fewer than 240,000 cybercrime domains the previous year.
Vixie was prophetic: the growth in cybercrime domains is almost all associated with maliciously registered cybercrime domains.
What Does This Mean to Me?
While the data says nothing about the percentage of total domains under management that are maliciously registered cybercrime domains, the more careful among us will want to be very cautious about any URL that refers to one of these top 25 TLDs. Blocking the whole TLD and then allowing exceptions where there is a specific business case, would be a prudent step that will help reduce the impact of cybercriminals’ efforts.
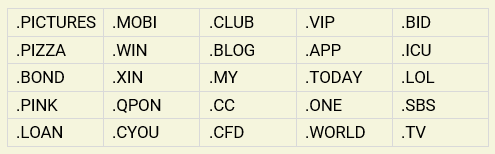
You can block entire TLDs at firewalls using regex pr URL filters (e.g. Fortinet, Cisco, Palo Alto), or by using a DNS Response Policy Zone (DNS RPZ). If you choose to do this, you could begin with any or all of these 25 TLDs:
We don’t recommend such action lightly. Only you can decide what measures will be most effective in reducing phishing, malware or spam threats. We recommend that you revisit which TLDs you block regularly, as cybercriminals historically strip mine TLDs and move to others if they find that their attacks have been blunted through blocking efforts. You can use our records repository at the Cybercrime Information Center to periodically review and update your list.