Reporting Domain Abuse: Experience and Assessment
Andy Malis
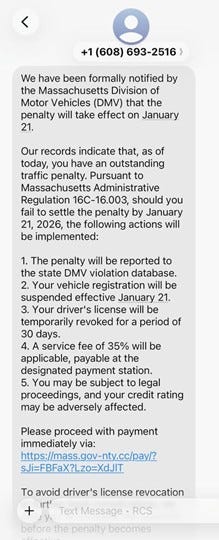
On January 21, I received the following text message:
I could tell right away that it was a fake phishing attempt. The Mass. DMV doesn’t send threatening text messages, nor do most any DMVs or RMVs in the US. Secondly, if you take a close look at the URL in the message, the domain name part of the URL is “mass.gov-nty.cc”. This name composition is a not-so-subtle attempt to look enough like the state’s official domain, “mass.gov”, to fool someone into clicking that URL. I did not, but if I had, I’m sure that it would have looked a lot like an official website. Of course, any credit card info I submitted to such a site would have exposed me to any amount of fraud. And I may have unintentionally downloaded malware onto my phone.
I could have just ignored the text and deleted it from my phone, but I wanted to do my bit to strike back against the bad guys. The first thing I did was to get some basic information about the website they tried to get me to click on.
This. Is. Domain. Abuse.
As I said above, the URL contains the domain name “mass.gov-nty.cc”. The really important part of that domain is the primary part – “gov-nty.cc”. The “.cc” part is the Top-Level Domain (TLD), and the “gov-nty” part is the primary string. If you regularly read Interisle’s Substack articles, you’ll be aware that “.cc” is one of the top TLDs used by phishers (for example, see the “Phisher Favorites” chart in Interisle’s Cybercrime Reported in January 2026, where .cc is the second-ranked TLD in recent use by phishers).
There are a number of websites one can use to look up a domain name and find out all kinds of information about it. The one that I prefer is Whois.com. I went there and typed in gov-nty.cc into the search box. In the results, I found that the domain name was registered on January 20 (just the day before I got the text message), the domain name was registered using a Singapore registrar, Gname.com, which is located in. The Whois information also contained an abuse email address listed for Gname.com, complaint@gname.com, so I decided to send in a complaint about the domain name.
My Experience: Reporting DNS Abuse (YMMV)
I sent the following email to complaint@gname.com:
Please be aware that the domain gov-nty.cc, for which you are the registrar, is being used for phishing abuse. See the URL in the enclosed screen shot.
I enclosed the screen shot of the text message at the top of this article. I then waited for a reply.
I did get a reply, but it wasn’t the one I wanted. Rather, I got an automated reply:
Please note that we do not accept or monitor abuse reports via email. A formal complaint must be submitted exclusively through our online reporting form.
Gname.com included the URL for their reporting form, so I went to the website, filled out the form, and uploaded the screen shot image. My next response from them was much more satisfying. They wrote back:
Your abuse report case (No.GW2026020401546836) has been processed and the results are as follows:
Domain Results
gov-nty.cc Client Hold
A clientHold domain status indicates that the registrar has suspended the domain, causing it to stop resolving in DNS. This action takes websites and emails offline. It is usually enacted due to non-payment, legal disputes, expired registration, or unverified contact details.
I’ll generously include criminal activity in the “legal disputes” category of this definition. So, the phisher’s website is now offline.
This counts as a small victory for the good guys.
Reporting Channels for Abusive Domains Are Important
Reporting channels give users and security professionals somewhere to turn and create a record that can inform registrars or TLD operators and incent action. But we should be honest about their limits: during the time that elapses from when a typical user like me identifies a weaponized domain, submits a complaint, the complaint is investigated, and is taken down, it is likely that many have already been victimized.
Necessary but not sufficient.
A system built mainly on after-the-fact reporting, however, will always be inherently reactive and inefficient no matter how responsive. It relies on users and security teams to play endless whack-a-mole, flagging one malicious registration at a time while new ones continue to appear. That may manage individual incidents, but it does little to reduce large scale abuse.
If we want to meaningfully reduce domain abuse and victimization, the focus has to move upstream. The key question isn’t just how fast we can remove bad domains, but how easily criminals can register and deploy them in the first place. Preventative, systemic approaches that reduce abusive registrations are critical, along with efficient mitigation processes.
Lessons Learned from This Small Victory
Lesson one. Don’t click on a URL you get in a text or email unless you are absolutely sure that it’s legitimate, especially if it is not from a source you know.
Lesson Two. The next time you get a phishing email or text, try taking some action yourself – it feels good, and it helps the community.